Table of Contents
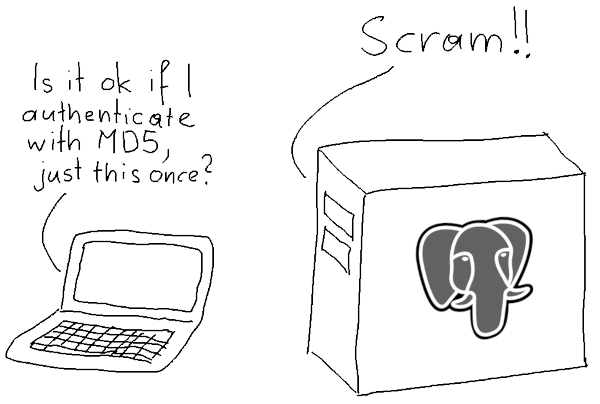
Since v10, PostgreSQL has provided support for scram-sha-256 for password hashing and authentication. This article describes how you can adapt your application safely.
scram-sha-256?PostgreSQL uses cryptographic hashing for two purposes:
Now, the MD5 hashing method has weaknesses that make it unsuitable for cryptography. In particular, it is too easy to construct a string with a given MD5 hash. These shortcomings do not apply to the way PostgreSQL uses MD5, but it still makes sense to use a better hashing algorithm:
Hence the introduction of scram-sha-256 support in v10. If you can, start using the new hashing method. The increased difficulty of brute force password attacks makes it worth the effort.
scram-sha-256There are two problems that make it hard to switch over from MD5 to scram-sha-256:
scram-sha-256.scram-sha-256 authentication, so authentication with older client software will fail.The error message you get with an old version of libpq when you attempt to connect to a server that requires scram-sha-256 authentication is:
|
1 |
authentication method 10 not supported |
An old JDBC driver will tell you:
|
1 |
The authentication type 10 is not supported. |
Old versions of Npgsql will come back with:
|
1 |
Authentication method not supported (Received: 10) |
scram-sha-256It is actually not difficult to convert to scram-sha-256, if you follow these guidelines:
Upgrade all PostgreSQL client software and drivers that are too old to support the new authentication method. This is a good idea anyway, as it is never smart to get stuck with old, unmaintained software.
password_encryption parameterEdit postgresql.conf and change the parameter to
|
1 |
password_encryption = scram-sha-256 |
Make sure you remove the hash (#) at the beginning of the line. Then reload the server by running
|
1 |
pg_ctl reload -D /postgres/datadir |
where /postgres/datadir is the PostgreSQL data directory. Alternatively, you can run this SQL statement:
|
1 |
SELECT pg_reload_conf(); |
Look into the log file to see if the reload was successful, and check the new value via SQL:
|
1 |
SHOW password_encryption; |
Note that even though you changed the parameter, the old MD5 passwords still work, as long as the authentication method in pg_hba.conf is set to md5.
All password authenticated users have to change their password. In psql, a superuser can change any user's password with
|
1 |
password user_name |
Even if the user sets the same password as before, the password will now be hashed with SHA-256. Before proceeding with the next step, examine the table pg_authid and make sure that it contains no more MD5 hashed passwords.
pg_hba.confThis step is not strictly necessary, because PostgreSQL will use scram-sha-256 authentication for scram-sha-256-hashed passwords, even if the authentication method is set to md5 in pg_hba.conf. This is a compatibility feature.
Still, you should adapt pg_hba.conf by replacing all occurrences of “md5” with “scram-sha-256”. That will prevent users who still have an old MD5 password from authenticating.
After that, reload the configuration as above. Then check the log file or examine the view pg_hba_file_rules to see if the reload was successful.
You can see from the above that it is not so difficult to change from md5 to scram-sha-256. The hard parts are that you have to set all the passwords again, and that you may have to upgrade the client software.
If you want to know how to protect yourself from common security problems, read Kaarel's blog or my article about SECURITY DEFINER functions.
In order to receive regular updates on important changes in PostgreSQL, subscribe to our newsletter, or follow us on Twitter, Facebook, or LinkedIn.
+43 (0) 2622 93022-0
office@cybertec.at
You are currently viewing a placeholder content from Facebook. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from X. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information
Thanks. As usual your posts are so interesting.
Hi Laurenz
Do you know how to get SCRAM-SHA-256 hash for known password?
I know just one option is to create "temporary" user with this password, select it from pg_shadow and then rollback. Maybe more elegant way exists?
No, I don't know a more elegant way.
You'd have to read the source. That would make a good blog post.
Why do you need to know the SCRAM secret for a password?